DORA Digital Operational Resilience Act (2026 Guide)

You open a meeting, and someone says, “We need to be DORA-compliant.” Half the room nods, half the room looks uncertain, and suddenly everyone is using the acronym as if it explains itself. That is a common starting point across banks, insurers, investment firms, and payment institutions. People know DORA matters, but many are still unclear on what the name really means, who it applies to, and what practical work sits behind it.
That is exactly why this guide exists. The dora digital operational resilience act is not just another label in EU regulation. It sets expectations for how financial entities manage ICT risk, report major incidents, test resilience, oversee third-party providers, and maintain operational continuity. In 2026, the focus is no longer just initial readiness. Supervisors increasingly want evidence that your processes work in practice.
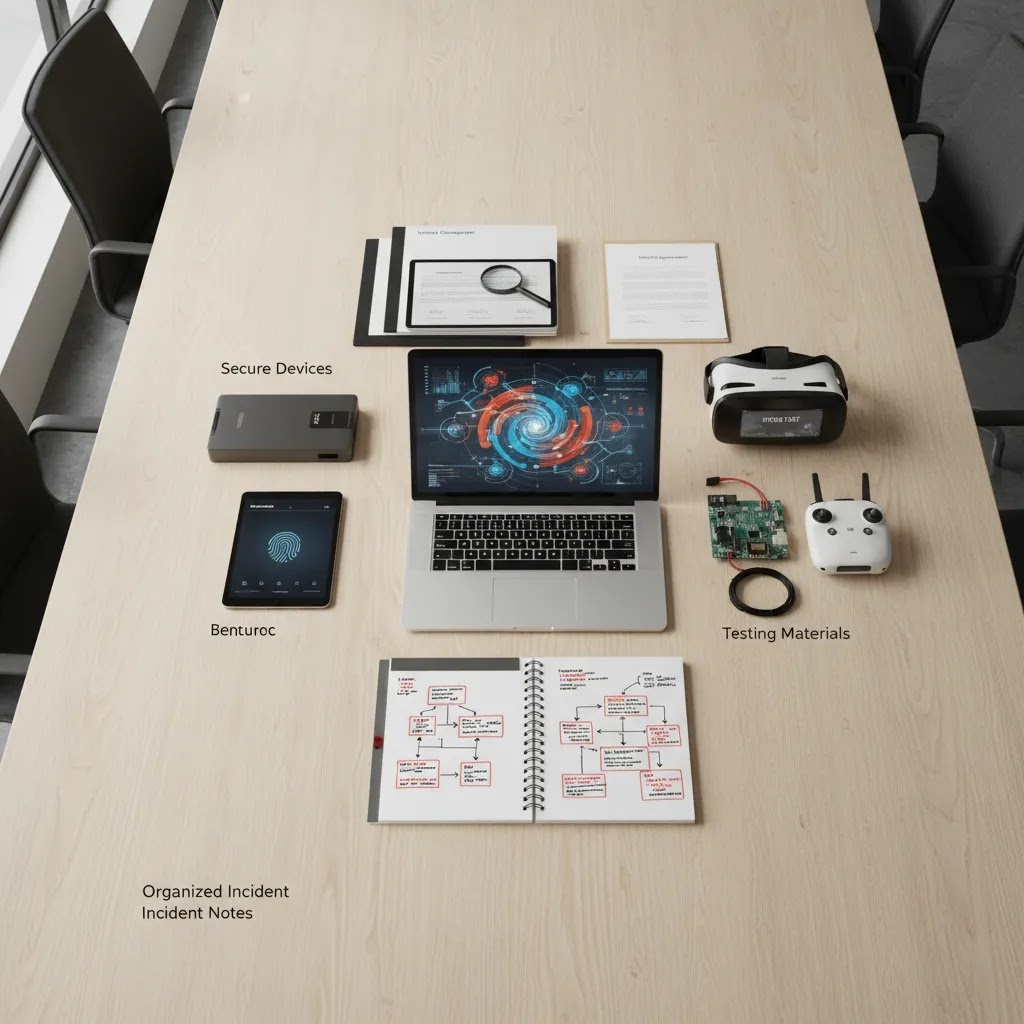
DORApp was built to simplify DORA compliance for EU financial institutions through a modular approach, turning complex regulatory requirements into structured, manageable workflows with auditable records and technically compliant reporting outputs. If you are still building your understanding of the basics, this article will help you get clear fast.
What DORA actually means
DORA stands for Digital Operational Resilience Act. Its full legal name is Regulation (EU) 2022/2554. If you have seen the phrase written as digital operational resilience act (dora) or dora (digital operational resilience act), those are simply two ways of expressing the same law.
At a practical level, DORA is an EU regulation designed to strengthen how financial entities prepare for, respond to, recover from, and learn from ICT-related disruptions. That includes cyber incidents, outages, third-party failures, and broader technology breakdowns that could interrupt important services.
If you want a broader foundation first, Dorapp also covers related concepts like what is digital resilience and the wider idea of what is digital resilience across sectors.
It is about operations, not just cybersecurity
One of the easiest mistakes is to treat DORA as a cyber rule only. Cybersecurity is part of the picture, but DORA is wider than that. It also deals with governance, continuity, testing, third-party dependencies, incident handling, and reporting quality.
Think of it this way: a financial entity may have strong security tools and still struggle with resilience if its provider register is incomplete, its incident escalation is unclear, or its evidence is scattered across spreadsheets, emails, and shared drives.
Why the acronym matters in practice
Acronyms can sound trivial, but with DORA, the wording tells you what regulators actually care about. “Digital” points to technology-enabled services and ICT dependencies. “Operational” shifts the focus from policy statements to day-to-day functioning. “Resilience” means your organization should continue operating, adapt under stress, and recover in a controlled way. “Act” signals that this is binding EU legislation, not a voluntary framework.
That wording helps explain why DORA reaches across so many functions. Compliance cannot handle it alone. Risk, IT, security, procurement, legal, and senior management usually all have a role.
For a closer definition-focused explainer, see Dorapp’s article on the what is digital operational resilience act question. You can also explore the related category page for DORA Fundamentals if you are building your basics.
Who DORA applies to
DORA applies to 20 categories of EU financial entities. That includes banks, insurers, investment firms, payment institutions, electronic money institutions, asset managers, crowdfunding service providers, and several other regulated entity types. The exact scope may depend on how your institution is classified under EU and national rules, so it is important to confirm this with your legal and compliance teams.
The regulation became applicable on 17 January 2025. By 2026, institutions are moving from launch-phase compliance work into ongoing evidence, governance, and supervisory review.
It also affects firms through third-party relationships
Even if you are not personally managing every DORA workstream, DORA may still affect your day-to-day responsibilities if you oversee cloud providers, software vendors, outsourcing contracts, or incident response.
From a regulatory standpoint, third-party dependencies are a major theme. Your institution is expected to understand what services it relies on, who provides them, and where concentration or subcontracting risk may sit. That is one reason the digital operational resilience act matters well beyond compliance teams.

The five pillars you need to know
DORA is commonly understood through five core pillars. If you can explain these clearly, you already have a much stronger grasp of the regulation than many teams do in their first workshops.
1. ICT risk management
You need a structured approach for identifying, assessing, managing, monitoring, and documenting ICT risk. This usually touches governance, controls, asset visibility, dependencies, and recovery planning.
2. ICT-related incident reporting
DORA creates expectations around classification, escalation, and reporting of major ICT-related incidents. Institutions need clear internal processes so reporting obligations can be met accurately and on time.
3. Digital operational resilience testing
Testing is how institutions demonstrate that controls and recovery arrangements work in practice. This can range from more regular assessments to advanced testing requirements for certain firms. If this area feels fuzzy, Dorapp has a dedicated explainer on digital operational resilience testing and a more practical next-step article on dora digital resilience testing.
4. ICT third-party risk management
This is where many teams feel the workload immediately. You need oversight of ICT third-party providers, contractual coverage, provider criticality, supply chain dependencies, and concentration risk. The Register of Information is a central part of this work.
5. Information sharing
DORA also recognizes voluntary information sharing arrangements related to cyber threat information and intelligence, subject to the applicable safeguards. This is often less discussed than the other pillars, but it remains part of the framework.
If you want a broader walk-through, the published post DORA Pillars Explained: Complete Breakdown (2026) is worth reading alongside this acronym guide.
What DORA requires under each pillar
The five pillars are a helpful mental model, but most teams still ask the same follow-up question: what does this mean I actually need to have in place? The answer depends on your entity type, your services, and your supervision context, so this is not a compliance checklist. It is a practical way to translate each pillar into the typical artifacts, operating processes, and evidence that supervisors often expect you to be able to show.
1) ICT risk management: governance plus the full lifecycle
Now, when it comes to ICT risk management, think in terms of two layers. The first is governance and accountability. The second is the end-to-end lifecycle of how you identify, protect, detect, respond, recover, learn, and communicate.
From a practical standpoint, the biggest gap is usually not that a policy is missing. It is that teams cannot show that the policy is embedded into day-to-day work, with consistent ownership and auditable evidence.
2) ICT-related incident reporting: a working classification and reporting workflow
DORA expects you to be able to detect, classify, escalate, and report major ICT-related incidents. In day-to-day terms, that typically means you need a workflow that can run fast under pressure, even when facts are incomplete.
Consider this: if your reporting process only works when the same two people are online, it is a key-person risk. DORA pushes institutions toward a more resilient operating model.
3) Digital operational resilience testing: a program, not one test
Testing under DORA is usually best understood as a calendar-backed program. You plan what you test, why you test it, what “good” looks like, and how you track remediation. Depending on your institution, this can include a mix of control testing, scenario exercises, technical assessments, and more advanced activities for certain firms.
The difference often comes down to whether testing outputs are usable for management decisions. A pile of test reports is not the same as a program with trends, accountability, and measurable follow-through.
4) ICT third-party risk management: oversight you can prove
This pillar is often where the workload becomes visible because it combines procurement realities with regulatory expectations. Most institutions need a structured way to assess provider criticality, negotiate and map contractual clauses, track subcontracting, and monitor concentration risk over time.
What many people overlook is that third-party risk is not only about the vendor. It is about your dependency chain, including subcontractors, and how quickly you can understand your exposure when something breaks.
5) Information sharing: guardrails that make it safe to participate
DORA recognizes voluntary cyber threat information sharing, but the key word is “safeguards.” In practice, institutions often need internal guardrails so sharing does not create new risk. That may include clarity on what can be shared, with whom, how it is handled, and who approves participation in any sharing arrangement.
For most small business owners and entrepreneurs reading DORA content, this pillar can feel abstract. For regulated financial entities, it typically becomes practical once you define participation, approvals, and evidence like you would for any other control activity.
How the pillars map to real workstreams
Here’s the thing, DORA usually becomes manageable once you assign each pillar to recurring workstreams with clear owners and a cadence. That often looks like:
If your goal is to reduce manual friction, a platform approach can help you turn these workstreams into structured workflows with audit trails and controlled outputs. That is the operating idea behind DORApp’s modular approach, especially for teams trying to move from document collections to repeatable execution.
What 2026 looks like for compliance teams
The reality is that 2026 is less about asking, “What is DORA?” and more about proving your institution can operate under it consistently. Regulators are increasingly focused on evidence quality, repeatable governance, and whether your records stand up under scrutiny.
Several developments shape that shift. The European Supervisory Authorities designated Critical Third-Party Providers in November 2025. Delegated Regulation (EU) 2025/532 introduced deeper subcontracting risk expectations. The ECB also finalized its Guide on outsourcing cloud services in July 2025, which adds practical context for institutions with material cloud dependencies.
The Register of Information became central fast
The first EU-level Register of Information submission deadline was 30 April 2025, using XBRL based on the DORA XBRL Data Point Model. In many institutions, that deadline exposed data quality issues, ownership gaps, and inconsistent supplier records.
Platforms like DORApp streamline the Register of Information process through modular workflows for importing existing records, maintaining data in a structured interface, enriching records from public sources, validating against reporting logic, and generating technical outputs from a proprietary data model that converts to XBRL. That does not replace legal judgment, but it may reduce a lot of administrative friction.
You can also browse the Digital Operational Resilience category for related explanations and implementation content.
Oversight of critical ICT third-party providers (CTPPs) and what it changes for you
By 2026, “critical third-party providers” stopped being a theoretical concept for many institutions. DORA includes a dedicated oversight framework for ICT third-party providers that are designated as critical at EU level. You are not expected to run that oversight yourself, but the existence of it can change what supervisors expect from you as a regulated firm.
Think of it this way: once a provider is under centralized oversight, your institution still carries responsibility for managing its own risk. The oversight framework may increase the amount of scrutiny around your dependency on that provider, how you manage concentration risk, and how credible your exit and continuity planning really is.
What the CTPP oversight concept often means in practice
For regulated firms, the practical implications typically show up in three places.
This does not mean every firm needs the same depth of controls. Requirements are typically shaped by proportionality, your business model, and supervisory expectations. The point is that the oversight environment raises the bar on evidence and clarity.
Practical implications for vendor management teams
What many people overlook is that CTPP oversight can expose weak spots in vendor management operations that were tolerated before. In many institutions, the gap is not the existence of a process, it is the consistency of execution and the quality of the records.
From a practical standpoint, this is where many teams either gain confidence or lose time. When dependency and contract data lives in too many places, you end up spending weeks just preparing for internal audit or supervisory questions.
Why the Register of Information matters even more as oversight matures
DORA’s Register of Information is not just a reporting requirement. It becomes the baseline dataset that helps you answer questions about dependencies, services, provider criticality, and subcontracting. If your register has gaps or inconsistent naming, it can be hard to produce a clear view of risk quickly.
The reality is that accurate dependency data often becomes more important over time. As oversight of critical providers matures, institutions that can produce structured, reliable records tend to have more control of the conversation. Institutions with fragmented records often end up in reactive mode.
Where teams usually get stuck
Most institutions do not struggle because the acronym is hard. They struggle because DORA connects many moving parts that used to live in separate teams.
Common friction points
What many people overlook is that DORA work often fails at the operating-model level, not the knowledge level. Teams may understand the words but still lack a controlled execution process.
That is where tools can help, if they fit the institution. With configurable workflows, audit trails, validation logic, and modular coverage, DORApp is one platform worth exploring for firms that want structured DORA operations rather than one-off document exercises. Dorapp’s founder-led background across FinTech, InsurTech, and RegTech also gives the brand a practical view of how regulated firms actually work, not just how frameworks look on paper.
How to read DORA more confidently
If you are new to this regulation, the best approach is to read DORA in layers. Start with the name and scope. Then understand the five pillars. Then map those pillars to your internal teams, data sources, and recurring processes.
From a practical standpoint, you do not need to master every technical standard in one sitting. You do need to know what questions to ask. For example:
It also helps to understand the policy background. If you want the longer regulatory story, see DORA European Commission Timeline and History (2026).
Here’s the thing, confidence usually comes from structure, not memorization. If your institution can connect obligations to owners, data, approvals, and reporting outputs, DORA becomes much more manageable.

How DORA is structured in the legal text
If you have opened Regulation (EU) 2022/2554 and felt lost, you are not alone. Legal text is not written for speed-reading, and DORA covers a lot of territory. One of the easiest ways to read it as a non-lawyer is to use its structure, in other words, to treat it like a map.
DORA is organized into chapters that mirror the way the regulation is implemented in real institutions: governance and ICT risk management, incident reporting, resilience testing, third-party risk, and information sharing. Once you see that layout, you can jump to the area that matches your role instead of reading linearly from start to finish.
A practical “table of contents” way to navigate DORA
Most teams benefit from a simple approach: start with the chapter that matches your immediate responsibilities, then expand outward. Typically:
This is a reading strategy, not compliance advice. Supervisory expectations can vary by entity type and national context, so your legal and compliance teams should still anchor decisions in the full set of applicable requirements and technical standards.
Why proportionality matters as an organizing principle
DORA is designed to apply across a wide range of financial entities. The difference often comes down to proportionality. In plain English, proportionality means the depth and formality of what you implement should generally reflect your size, risk profile, and complexity. Smaller or less complex firms are not typically expected to mirror the exact same operating model as the largest institutions.
That said, proportionality is not a shortcut. It usually means you need a clear rationale for your approach, plus evidence that your controls work for your business and your ICT dependency profile.
What to read first if you want faster clarity
If your goal is to get oriented quickly, start by identifying three things in the text: (1) who is in scope, (2) which obligations are ongoing processes versus one-time setup, and (3) what evidence you would need to show that the process operates. Once you can answer those, the regulation becomes less intimidating, and discussions across IT, risk, compliance, and procurement become more grounded.
Disclaimer: The information in this article is intended for general informational and educational purposes only. It does not constitute professional technical, legal, financial, or regulatory advice. Website performance outcomes, platform capabilities, and business results will vary depending on your specific circumstances, goals, and implementation. Always evaluate tools and platforms based on your own needs and, where relevant, seek professional guidance.
Regulatory note: This article is for informational purposes only and does not constitute financial, legal, or regulatory advice. DORA compliance requirements may vary based on your institution type, size, and national regulatory framework. Content referencing regulated industries is provided for general context only and should not be interpreted as legal, regulatory, compliance, or financial advice. If you operate in a regulated sector, always consult qualified financial, legal, and compliance professionals for guidance specific to your situation.
Frequently Asked Questions
What does DORA stand for in full?
DORA stands for Digital Operational Resilience Act. The full legal reference is Regulation (EU) 2022/2554. In practice, people often use the acronym because it is shorter, but the full name is useful because it tells you the focus of the regulation: digital systems, operational continuity, and resilience. If you work in compliance, IT, risk, procurement, or internal audit, knowing the full name helps you explain why DORA reaches across multiple teams instead of sitting with one department alone.
What is the main goal of DORA (what problem is it trying to solve)?
The main goal of DORA is to raise the baseline for operational resilience across the EU financial sector, especially for technology-driven disruptions. In practical terms, it is trying to reduce situations where outages, cyber incidents, or third-party failures cause serious disruption to important financial services. DORA does this by setting expectations for ICT risk management, incident reporting, resilience testing, third-party oversight, and evidence that these processes work in real operating conditions.
What are “ICT” risks and incidents under DORA in plain English?
Under DORA, “ICT” refers to information and communication technology, basically the systems, networks, applications, infrastructure, and service providers that keep financial services running. ICT risks and incidents can include things like system outages, failed deployments, cyber attacks, data corruption, provider disruptions, and other technology-related events that affect availability, integrity, confidentiality, or continuity. Whether a specific event becomes a reportable “major” incident depends on the classification criteria and your supervisory context, so institutions typically define clear internal workflows and decision rights.
Is DORA only about cybersecurity?
No. Cybersecurity is part of DORA, but DORA is broader than cyber alone. It covers ICT risk management, major incident reporting, resilience testing, third-party risk oversight, and certain information-sharing arrangements. A firm may have strong cyber tools and still be weak from a DORA perspective if it cannot evidence provider oversight, testing outcomes, or reporting governance. That is why many institutions treat DORA as an operational resilience framework with a strong technology core, not just as a security regulation.
Who needs to comply with DORA?
DORA applies to 20 categories of EU financial entities. This includes a wide range of firms such as banks, insurers, investment firms, payment institutions, and other regulated financial organizations. Whether your legal entity is directly in scope may depend on your exact regulatory classification and local implementation context. If you are unsure, your legal and compliance teams should confirm it formally. Even where a team is not the official owner of DORA, staff involved in ICT sourcing, contracts, incidents, or risk documentation may still be affected in daily work.
When did DORA start applying?
DORA became applicable on 17 January 2025. That date marked the beginning of active compliance expectations across in-scope financial entities. In 2026, many institutions are moving beyond first-phase readiness and into ongoing supervisory scrutiny, recurring reporting, and proof-of-compliance work. In other words, the question is no longer just whether a policy exists, but whether the institution can show controlled execution, evidence quality, and repeatable resilience processes in real operating conditions.
What are the five pillars of DORA?
The five pillars are ICT risk management, ICT-related incident reporting, digital operational resilience testing, ICT third-party risk management, and information sharing. These pillars are a practical way to organize the regulation and explain it internally. They also help institutions assign ownership across teams. For example, testing may sit with IT and security, while provider oversight often involves procurement, legal, and compliance. The pillars do not replace the legal text, but they are a very useful operational model for planning implementation and governance.
What is a critical ICT third-party provider (CTPP) under DORA?
A critical ICT third-party provider is an ICT service provider that can be designated as “critical” at EU level under DORA, based on criteria set in the framework. The key point for financial entities is that dependency on a critical provider often brings more scrutiny around concentration risk, subcontracting visibility, and exit planning. The oversight of these providers is handled through the DORA oversight framework, but regulated firms still need to manage their own risks and maintain clear evidence of third-party oversight.
What is the proportionality principle in DORA, and how does it affect smaller firms?
Proportionality means DORA requirements are typically applied in a way that reflects the size, complexity, and risk profile of the entity. For smaller or less complex firms, this often affects how formal and extensive certain processes and documentation need to be. It does not remove the obligation to manage ICT risk, report incidents, test resilience, and oversee providers, but it may influence the depth, frequency, and governance layers expected by supervisors. Because proportionality can be interpreted differently across entity types and jurisdictions, firms usually confirm their approach with their compliance and legal teams.
What is the Register of Information under DORA?
The Register of Information is the mandatory record of ICT third-party service arrangements that in-scope institutions must maintain under DORA. It is not just a supplier list. It typically requires structured information about services, providers, dependencies, contracts, and links to critical or important functions. The first EU-level submission deadline was 30 April 2025, and the reporting format uses XBRL based on the DORA Data Point Model. Maintaining this register accurately is one of the most practical and time-consuming parts of DORA compliance.
Does DORA require XBRL reporting?
Yes, for certain EU-level submissions such as the Register of Information, the reporting format is XBRL based on the DORA XBRL Data Point Model. This matters because even teams that understand the business content may struggle with technical submission formats. In practice, many firms need a controlled way to map business records into technically valid reporting outputs. DORApp approaches this through a proprietary data model that converts into XBRL, which may be helpful for institutions trying to reduce manual transformation work and reporting friction.
What changed for DORA in 2026?
2026 is shaped by a shift from initial compliance to evidence-based supervision. Regulators are expected to focus more on whether institutions can prove their resilience processes operate consistently. Recent context includes the November 2025 designation of Critical Third-Party Providers, the added subcontracting risk depth introduced by Delegated Regulation (EU) 2025/532, and ongoing scrutiny of cloud outsourcing arrangements. For many institutions, this means better data quality, stronger workflows, and clearer ownership matter just as much as having the right policy documents.
Can software make an institution DORA-compliant?
No software can automatically make an institution compliant on its own. DORA is a legal and operational framework, so compliance depends on governance, decisions, controls, evidence, and institution-specific implementation. What software can do is support those processes by improving structure, validation, documentation, reporting, and audit readiness. That distinction matters. Under DORA, the requirement comes from the regulation itself. A platform like DORApp may help teams execute their obligations more efficiently, but it does not replace legal interpretation or management responsibility.
Where should a beginner start with DORA?
Start with three basics. First, understand the full meaning and scope of the Digital Operational Resilience Act. Second, learn the five pillars so you can organize the regulation mentally. Third, map those pillars to your institution’s teams, systems, and third-party relationships. That gives you a practical lens quickly. After that, move into the Register of Information, incident reporting flows, and testing expectations. If you prefer structured reading, Dorapp’s DORA and digital operational resilience articles are a good place to build that foundation without getting lost in unnecessary jargon.
Key Takeaways
Conclusion
The dora digital operational resilience act sounds complicated at first mostly because people often encounter the acronym before they understand the operating model behind it. Once you break it down, the picture becomes clearer. DORA is about how financial entities prepare for disruption, manage ICT risk, oversee third parties, test resilience, and keep evidence that stands up under regulatory review.
If you are early in your learning process, focus on the fundamentals first: scope, pillars, ownership, and the Register of Information. That foundation makes every deeper topic easier, whether you are reviewing contracts, preparing reports, or planning resilience testing. If you want a more structured path, explore Dorapp’s related DORA and digital operational resilience resources, or see how DORApp approaches real-world compliance workflows. You can also book a demo if your team wants a practical look at structured DORA operations without relying on scattered spreadsheets and manual reporting work.
About the Author
Matevž Rostaher is Co-Founder and Product Owner of DORApp. He brings deep experience in building secure and compliant ICT solutions for the financial sector and is positioned by DORApp as an expert trusted by financial institutions on complex regulatory and operational challenges. DORApp’s own webinar materials list him as CEO and Co-Founder of Skupina Novum d.o.o. and CEO and Co-Founder of FJA OdaTeam d.o.o. His articles should carry the voice of someone who understands not just compliance requirements, but the systems and delivery realities behind them.